Cloud EDR
Cloud Threat Detection & Response
Protect Your Critical Cloud Assets from Misconfigurations and Advanced Cyber Threats As businesses increasingly shift to cloud environments, securing cloud-native infrastructure has become critical. DefenceRabbit’s Cloud Threat Detection & Response service is designed to safeguard your cloud workloads, storage, and applications from evolving threats including misconfigurations, data exfiltration, and sophisticated malware attacks. conver this into single one

Why CLOUD EDR
Why choose Cloud Detection and Response ?
In today’s cyber threat landscape, real-time threat detection and response isn’t optional it’s essential. Yet, many small to mid-sized managed service providers (MSPs) lack the budget or manpower for a fully staffed 24/7 Security Operations Center (SOC). This results in delayed responses to critical threats, giving attackers the window they need to exploit vulnerabilities and infiltrate networks. That’s where Cloud Endpoint Detection and Response (Cloud EDR) comes in. With DefenceRabbit’s Cloud Detection and Response, powered by advanced AI and backed by a dedicated 24/7 SOC, you can ensure your customers’ networks remain secure around the clock weekends, holidays, and late nights included.
Incomplete Insights Lead to Incomplete Cloud Security
Traditional threat detection tools were never designed for the complexities of modern cloud environments. Most rely heavily on agents to collect telemetry from workloads offering only partial visibility. This results in critical blind spots across your cloud infrastructure, including workloads, configurations, user identities, and control plane activities.
Solutions like EDR, TDR, and even some XDR platforms are effective at identifying risks at the cloud workload level. However, they often fail to monitor the control plane, leaving organizations blind to threats like identity-based attacks, where compromised user credentials are used to access cloud resources undetected.
Many current Cloud Detection and Response (CDR) tools are retrofitted versions of traditional on-premise solutions. These adaptations lack native cloud telemetry and miss crucial contextual data, making it harder to detect advanced threats in cloud-native environments.
Agent-based detection tools require security agents installed on every asset, a model that’s impractical in dynamic, containerized, or serverless cloud architectures. This leaves organizations vulnerable to threats that lie outside of agent coverage.
Key Capabilities

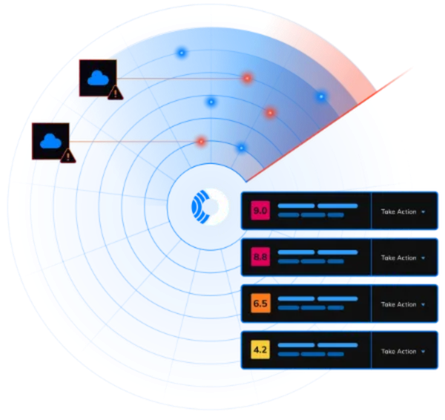
Detect Suspicious Activity In Your Cloud

Risk-Based Prioritization Of Suspicious Events

Combine Single Events into Cohesive Attack Narratives

Automated Response Against Malicious Activity
Our WorkFlow
Proactive Threat Detection
Real-time monitoring of cloud environments for suspicious activities and anomalies. Advanced threat intelligence to identify emerging threats and vulnerabilities.
Rapid Incident Response
Automated incident response workflows to contain threats quickly and effectively. Integration with security orchestration, automation, and response (SOAR) tools for streamlined incident management.
Comprehensive Threat Prevention
Vulnerability scanning and patching to address security weaknesses. Integration with cloud security posture management (CSPM) tools for proactive risk mitigation.
Ready to Cloud Threat Detection & Response
Ensure your 24/7 cloud gets top-notch protection around the clock. Contact us today.
FAQ’s
Frequently Asked Questions
What is Cloud Threat Detection and Response?
Cloud Threat Detection and Response (CDR) is a critical cybersecurity practice focused on identifying, analyzing, and mitigating threats within cloud environments. As organizations increasingly adopt cloud infrastructure to store data and run applications, ensuring these environments are secure is more important than ever.CDR continuously monitors cloud activity such as user behavior, API calls, network traffic, and system configurations to detect signs of malicious activity or misconfigurations. It enables real-time threat detection, automated responses, and deep visibility into your cloud infrastructure.By integrating AI-driven analytics and behavior-based monitoring, cloud threat detection and response empowers security teams to stay ahead of sophisticated cyberattacks, reduce response time, and prevent data breaches across multi-cloud or hybrid cloud environments.
Why is Cloud Threat Detection and Response important for organizations?
Cloud Threat Detection and Response is essential for organizations because it plays a critical role in safeguarding sensitive data and maintaining operational resilience in today’s digital-first world.
• Prevents data breaches by identifying and neutralizing threats before they cause damage.
• Blocks unauthorized access to sensitive applications, systems, and information.
• Ensures business continuity by minimizing downtime and service disruptions caused by cyber incidents.
• Maintains compliance with industry regulations and cybersecurity frameworks such as GDPR, HIPAA, ISO 27001, and more.
• Protects brand reputation by reducing the risk of publicized security breaches.
With cloud adoption accelerating, having a strong Cloud Threat Detection and Response strategy is no longer optional it’s a necessity for organizations aiming to stay secure, compliant, and competitive.
What Is Cloud Threat Detection And Response?
Cloud Threat Detection and Response (TDR) is a proactive cybersecurity strategy designed to detect, analyze, and respond to threats targeting cloud-based environments like Microsoft Azure, AWS, and Google Cloud.Unlike traditional security tools, Cloud TDR leverages machine learning, behavioral analytics, and real-time threat intelligence to continuously monitor cloud infrastructure for suspicious or malicious activity. It provides visibility into cloud workloads, user behavior, configurations, and API activity areas where conventional security tools often fall short.
How Does Cloud TDR Security Differ From Traditional TDR Security?
As organizations shift their infrastructure to the cloud, they encounter a new set of attack surfaces, evolving threats, and complex security challenges that traditional security tools aren’t equipped to handle. That’s where Cloud Threat Detection and Response (Cloud TDR) steps in.Unlike traditional TDR, which is typically designed for on-premises environments, Cloud TDR is purpose-built to secure cloud-native applications, services, and infrastructure. Here’s how they differ:
- Cloud-Native Visibility: Cloud TDR provides real-time monitoring of dynamic cloud assets such as containers, serverless functions, and virtual machines unlike traditional TDR which focuses mainly on fixed, on-prem assets.
- Identity & Access Monitoring: In cloud environments, identity is the new perimeter. Cloud TDR tracks user behavior, access controls, and privileges, detecting threats like compromised accounts something often missed by traditional solutions.
- API & Configuration Security: Cloud TDR tools monitor misconfigurations, exposed APIs, and insecure permissions across services like AWS, Azure, and Google Cloud. Traditional tools rarely offer this visibility.
- Elastic Scalability: Cloud TDR solutions scale automatically with your cloud footprint, adapting to growing workloads while traditional TDR often requires manual provisioning and can struggle with cloud elasticity.
- Agentless & Agent-Based Integration: Cloud TDR combines agentless scanning and agent-based detection for full-stack visibility. Traditional TDR typically depends on agents installed on endpoints.
