Red team assessments are becoming increasingly vital for strengthening cybersecurity in 2025. By simulating realistic attack scenarios, these assessments unveil potential vulnerabilities that traditional methods often miss. Organizations can identify weaknesses across people, processes, and technologies while evaluating their detection and response capabilities. The methodology includes a thorough planning phase, reconnaissance to gather intelligence, and exploitation techniques that encompass both technical and social engineering elements. Real-world applications demonstrate clear benefits: organizations can proactively fortify defenses before threats exploit weak points. As providers like DefenceRabbit.com focus on these advanced solutions, the importance of red teaming as a cornerstone of cyber resilience cannot be overstated.
Table of Contents
- How Red Teaming Works in 2025
- Benefits of Red Team Assessments
- Red Team Assessment Methodology
- Real-World Applications of Red Teaming
- Investing in Red Team Assessments
- Frequently Asked Questions
How Red Teaming Works in 2025
 Credits: reddit.com
Credits: reddit.com
Red teaming in 2025 takes a giant leap forward, blending traditional tactics with cutting-edge technology. By imitating real-world attackers, red teams provide a clear, realistic view of the threats that organizations face. They don’t just poke at the surface but delve deep into the interconnected systems, human behaviors, and processes that could be exploited. This year, the integration of AI and machine learning revolutionizes how these teams analyze attack patterns, making simulations more sophisticated and accurate than ever.
The collaboration between red teams and blue teams (the defenders) is crucial. This teamwork enhances the overall security posture, transforming the way organizations respond to threats. Tailoring assessments to specific industries allows red teams to address unique vulnerabilities, ensuring that no stone is left unturned. As regulatory requirements evolve, companies increasingly rely on red teaming to demonstrate compliance and showcase their commitment to security.
Continuous red teaming emerges as a best practice, shifting the paradigm from one-time evaluations to ongoing assessments. This approach allows organizations to adapt swiftly to new threats with real-time feedback from red team exercises. Moreover, the diverse skill sets within red teams, ranging from technical hackers to social engineers, enable comprehensive assessments that cover every angle of potential attacks.
With the increasing adoption of cloud environments, red teams now focus on protecting digital assets in hybrid infrastructures, ensuring that security measures are robust and effective. The findings from red team assessments are not just reports; they form the backbone of an organization’s security strategy, guiding effective remediation and continuous improvement. This holistic view of security empowers organizations to stay one step ahead in the ever-evolving landscape of cyber threats.
Benefits of Red Team Assessments
 Credits: twingate.com
Credits: twingate.com
Red team assessments offer numerous advantages that significantly enhance an organization’s cybersecurity posture. By conducting hands-on testing, these assessments increase awareness of security weaknesses, allowing teams to see where their defenses falter. This realistic approach not only uncovers vulnerabilities but also enhances incident response capabilities by revealing gaps in current processes and technologies. Engaging in simulated attack scenarios fosters a culture of security, encouraging collaboration across departments as various teams work together to address identified risks. Moreover, organizations can prioritize their security investments based on actual risk exposure, ensuring resources are allocated where they are most needed.
The measurable outcomes from red team assessments provide valuable insights that can be communicated to stakeholders, leading to improved decision-making. This process also facilitates better training for employees, empowering them to recognize and react to social engineering attempts, a common threat in today’s landscape. By thoroughly evaluating external connections, these assessments strengthen vendor and third-party risk management, ensuring that all potential entry points are secured. Additionally, red team insights drive innovation in security practices, as organizations learn from their experiences and adapt their strategies accordingly. Ultimately, red team assessments support continuous improvement in security posture, making organizations more resilient to future attacks and better equipped to navigate an ever-evolving threat landscape.
| Benefit | Description |
|---|---|
| Realistic Threat Simulation | Red teams mimic actual attack scenarios, revealing how organizations respond to sophisticated threats. |
| Identification of Vulnerabilities | Uncovers complex vulnerabilities within interconnected systems, processes, and human factors. |
| Enhanced Detection and Response | Evaluates detection mechanisms and response capabilities, highlighting gaps in security operations. |
| Training for Security Teams | Helps security professionals understand vulnerabilities and improve skills in monitoring and responding to threats. |
Red Team Assessment Methodology
 Credits: wesecureapp.com
Credits: wesecureapp.com
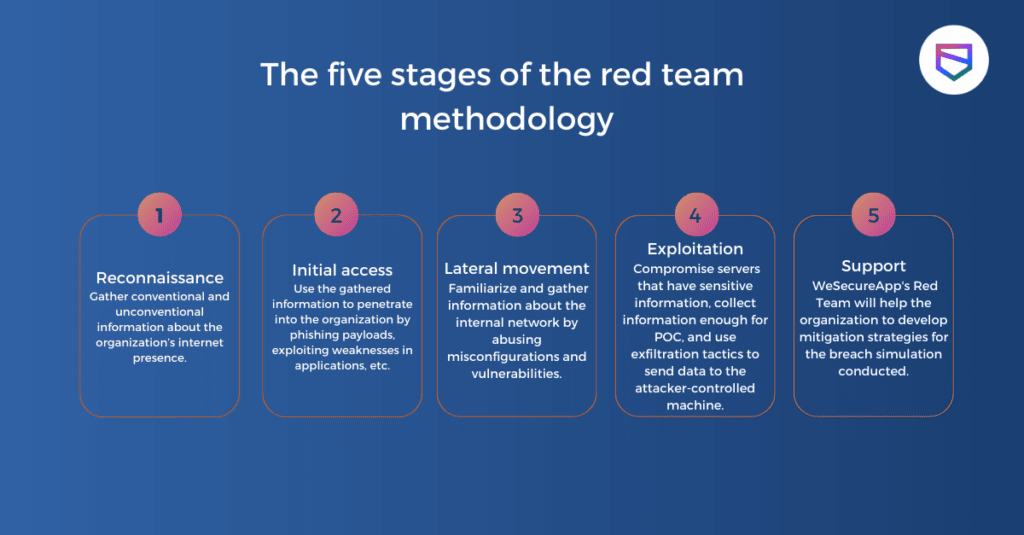
Red team assessments employ a structured methodology that is both innovative and effective in identifying vulnerabilities. The process starts with the identification of critical assets and processes, allowing teams to focus their efforts on areas that matter the most. Utilizing a blend of automated tools and manual techniques ensures a thorough testing of potential weaknesses. This dual approach enhances the depth of the assessments, revealing not just superficial flaws but also underlying issues that could be exploited.
Effective communication between the red and blue teams is crucial, creating opportunities for learning and growth. By incorporating threat intelligence into the assessment strategies, red teams can tailor their focus to current and emerging threats, making the evaluations more relevant. Moreover, incorporating both physical and cyber attack simulations provides a comprehensive view of an organization’s security posture, preparing teams for any scenario.
Tabletop exercises further enhance preparedness, allowing teams to practice their responses to incidents in a controlled environment. The results of these assessments are meticulously analyzed to generate actionable insights, which are essential for refining security strategies. Regular updates to the assessment methodologies keep pace with the rapidly evolving threat landscape, ensuring organizations remain one step ahead. Feedback loops are also vital, enabling teams to refine future assessments based on prior experiences, promoting a culture of continuous improvement. Sharing findings across the organization fosters a learning environment that reinforces a collective commitment to security.
Real-World Applications of Red Teaming
Red team assessments are proving to be a game-changer across various sectors in 2025. For instance, insurance companies are now leveraging these assessments to pinpoint client vulnerabilities, allowing them to fine-tune policy offerings tailored to real risks rather than generic ones. Similarly, government entities are utilizing red teaming to rigorously test the security of critical infrastructure against increasingly sophisticated cyber threats, ensuring national safety and resilience.
In the education sector, institutions are adopting red team assessments to bolster protections around student data while enhancing campus security protocols. Financial institutions are gaining invaluable insights from these engagements, which help them bolster defenses against fraud and cyber attacks that threaten their operations and customer trust. Retailers, too, are conducting red teaming to safeguard customer data and improve transaction security on their e-commerce platforms, ensuring that online shopping remains a secure experience.
Manufacturers are not left behind; they are employing red team exercises to secure supply chains and protect intellectual property from the ever-present cyber threats. Healthcare organizations are implementing these assessments to guarantee patient data security and ensure compliance with regulations like HIPAA, which is crucial in maintaining trust in an increasingly digital healthcare landscape. Technology companies are also on board, using red team assessments to identify vulnerabilities in new products before they hit the market, thus preventing potential breaches before they can occur.
Energy sector firms are leveraging red teaming to protect national grid systems from cyber threats, ensuring uninterrupted power supply and national security. Even non-profits are getting in on the action, adopting red team assessments to protect donor information and mission-critical data, thereby maintaining the integrity and trust of their operations. As these real-world applications show, red teaming is not just about testing security, it’s about transforming how organizations view and manage their cybersecurity posture.
Investing in Red Team Assessments
Organizations looking to bolster their cybersecurity posture should consider investing in red team assessments as a strategic priority. Starting small allows teams to gradually increase the complexity and scope of assessments as they mature, ensuring that they adapt effectively to emerging threats. Budgeting for these assessments should align with the overall cybersecurity strategy and risk management goals, focusing on areas that are most vulnerable. By preventing costly breaches and minimizing downtime, investing in red teaming can result in significant cost savings over time.
Collaborating with cybersecurity firms can provide organizations with the expertise and resources needed for effective red team assessments. These partnerships can lead to shared insights and cost reductions, especially when engaging in collaborative assessments with other organizations. To secure ongoing funding and support from leadership, demonstrating a clear return on investment (ROI) is essential. Organizations can also explore government grants or initiatives aimed at enhancing cybersecurity, which can further offset costs.
Prioritizing red team assessments based on risk exposure helps maximize the value of the investment, as it targets the most pressing vulnerabilities. Regularly reviewing and updating assessment contracts ensures that they remain valuable and adaptable to the ever-evolving threat landscape. Additionally, incorporating lessons learned from assessments into training programs can greatly enhance security awareness among staff, ultimately contributing to a more robust defense against cyber threats.
Frequently Asked Questions
What exactly is a Red Team assessment?
A Red Team assessment is a simulated cyber attack on an organization, meant to test and improve its security. It helps identify weaknesses and vulnerabilities in the system.
How does a Red Team assessment boost our cybersecurity?
It boosts cybersecurity by exposing flaws that regular security measures might miss, allowing organizations to strengthen their defenses and be better prepared for real attacks.
Who typically conducts these Red Team assessments?
These assessments are usually carried out by skilled cybersecurity professionals known as Red Teamers, who simulate attacks using various tactics and tools.
What types of threats do Red Team assessments focus on?
They focus on a range of threats, including phishing attempts, network vulnerabilities, and social engineering tactics, to mimic what actual attackers might do.
How often should our organization have a Red Team assessment?
It’s generally recommended to conduct these assessments at least once a year, or more frequently if there are significant changes in your organization or its technology.
TL;DR In 2025, red team assessments are essential for bolstering cybersecurity. They simulate real-world attacks, uncover complex vulnerabilities, and enhance detection and response capabilities. The methodology involves meticulous planning, reconnaissance, exploitation, and thorough reporting. Real-world applications reveal the need for improved security measures, showcasing red team engagements as crucial for proactive defense. Investing in these assessments helps organizations comply with regulations and build confidence in their security posture, making them a vital aspect of modern cybersecurity strategy.

